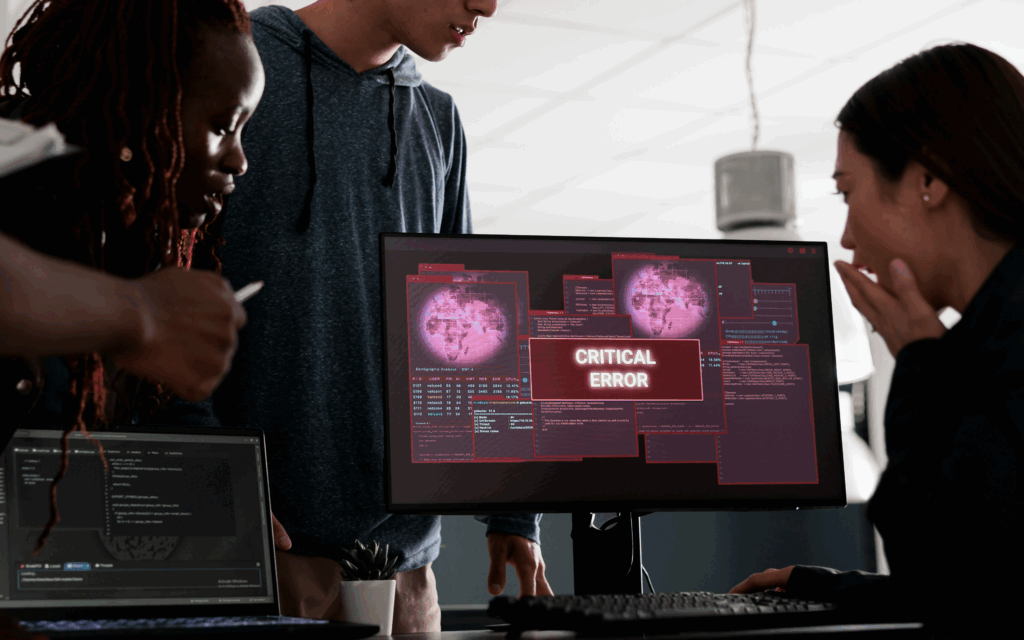
What Happens After Clicking a Phishing Link? The Business Risk Most Organizations Miss
Firewalls are stronger. Email filtering is smarter. Multi-factor authentication is widely deployed. Yet phishing remains the leading cause of security incidents across organizations of every size. Why? Because modern attacks are designed to bypass technology by targeting people — and the tools available to attackers are evolving faster than most organizations realize. Security controls continue […]
What Happens After Clicking a Phishing Link? The Business Risk Most Organizations Miss Read More »
Blog